
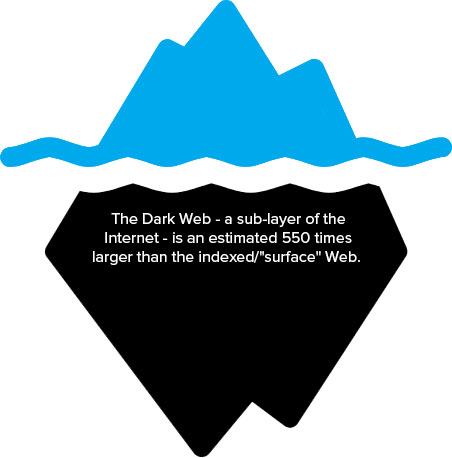
Did you know that the sites you access using traditional search engines like Google and Bing are only the tip of the iceberg when it comes to the Internet? The Dark Web - a sub-layer of the Internet - is an estimated 550 times larger than the indexed or "surface" Web. In this sub-layer, users can remain anonymous, and, as a result, it's a hotbed of illegal activity. One of the main reasons cybercriminals browse the Dark Web is to buy and sell stolen credentials that they can use to hack into accounts and access sensitive data.
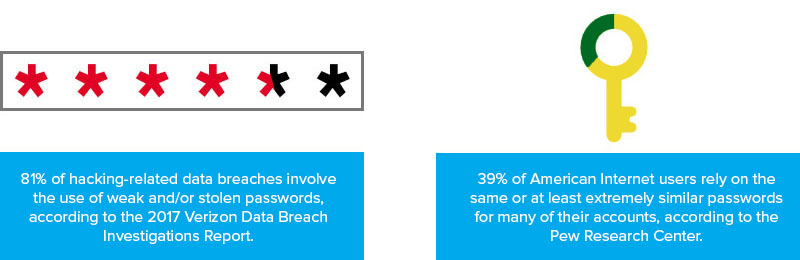
Having your employees' credentials distributed on the Dark Web can prove disastrous for your organization. The majority (81%) of hacking-related data breaches involve the use of weak and/or stolen passwords, according to the 2017 Verizon Data Breach Investigations Report. Additionally, one password can often open the door to multiple accounts and applications: 39% of American Internet users rely on the same or at least extremely similar passwords for many of their accounts, according to the Pew Research Center.
Fortunately, it's possible to scan the Dark Web and detect credential theft before it leads to data breaches and other crimes. With our monitoring solution, we can shed some light on the corners of the Dark Web and let you know if your information has been compromised. Using both human and artificial intelligence, we can search for stolen email addresses, passwords, and other confidential data in the following places:
- Private sites
- Botnets
- Peer-to-peer networks
- Internet relay chat (IRC) channels
- Black market websites
- Social media
- Hidden chatrooms
Our solution allows your business to leverage comprehensive logging and reporting abilities to identify and track incidents, as well as help establish policies to reduce the risk of similar security issues occurring in the future. Dark Web monitoring services from Stratosphere offer a number of benefits for your business, including the following:
- Real-time awareness and immediate notification of credential theft.
- Prevention of data leaks before they occur.
- Access to advanced credential monitoring abilities used by Fortune 500 companies.
- Capability to scan the Dark Web without connecting company software or hardware to high-risk Dark Web services (e.g., Tor, I2P, and Freenet).
In combination with a multilayered approach to IT security (including security awareness training, multi-factor authentication, vulnerability and patch management, and other solutions), our Dark Web monitoring services can significantly reduce your risk of experiencing a data breach.
Next Steps
To learn more about Dark Web monitoring and other managed cybersecurity solutions, please contact our expert team by calling 877-599-3999 or emailing sales@stratospherenetworks.com.
Contact StratosphereFind out how Stratosphere helped a client with their IT environment.
Read Case Study