 If you haven’t already experienced a data breach, odds are good that you will soon. In the fiscal year 2018, more than half (58 percent) of small and medium-sized businesses experienced a data breach, according to a report from the Ponemon Institute and Keeper Security. Hackers develop new techniques and release new malware daily, making it difficult to keep IT security defenses up-to-date.
If you haven’t already experienced a data breach, odds are good that you will soon. In the fiscal year 2018, more than half (58 percent) of small and medium-sized businesses experienced a data breach, according to a report from the Ponemon Institute and Keeper Security. Hackers develop new techniques and release new malware daily, making it difficult to keep IT security defenses up-to-date.
Preventing breaches from occurring in the first place with a proactive and comprehensive approach to cybersecurity is ideal. However, what do you do when your efforts to safeguard your organization’s data fail? If you’re seeking advice in the wake of an IT security incident, taking the following steps will help you control the damage and minimize your breach risk in the future.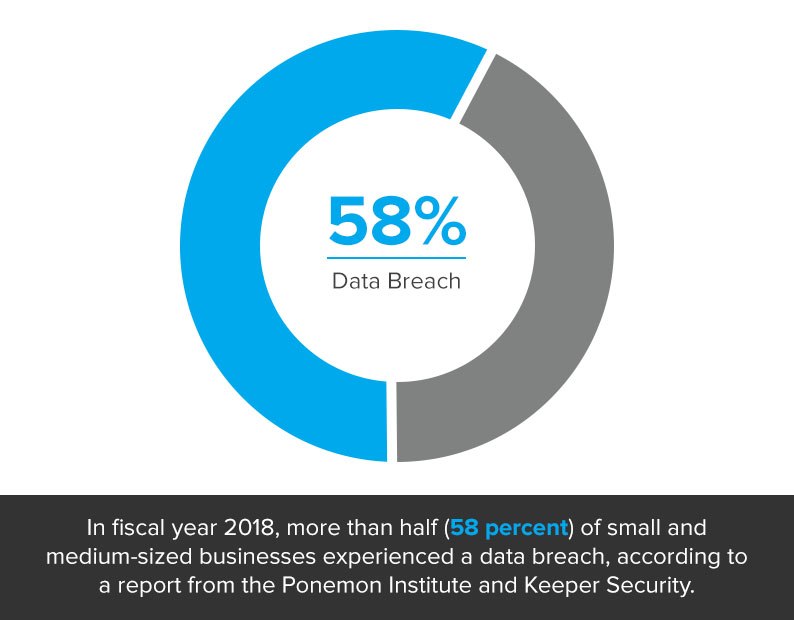
1. Preserve evidence. After you discover a breach has occurred, your first step should be to preserve evidence of the incident and manage the chain of custody to lower the odds that it will be tampered with or destroyed. This is key to facilitate an investigation of the breach and shed light on details such as how much data was exposed.
2. Notify your insurance. Hopefully your organization has cyber liability insurance that covers data breaches. Let them know about the incident.
3. Carry out your incident response plan. As part of your IT security strategy, you should already have an incident response plan in place. If you need assistance designing and executing a plan, Stratosphere’s team of cybersecurity experts can help.
4. Notify the proper personnel. Ensure that everyone within your organization who should know about the data breach is aware of what’s happening. In addition to an incident response plan, you should also assemble a response team, according to the credit bureau Experian.
Your incident response team should include people from the following departments/areas of expertise:
- Executive leadership
- HR
- Legal affairs
- PR
- IT
- Customer service
Additionally, you might want to enlist the services of external personnel, such as forensic specialists, legal counsel and a data breach resolution partner, according to Experian.
5. Inform authorities and/or regulatory governing bodies. Because data breaches can potentially affect government security, public safety and the economy, a growing number of states have passed cybersecurity regulations. Make sure you comply with those laws – as well as any industry-specific regulations such as HIPAA – and inform law enforcement and any relevant regulatory entities about the incident.
6. Take the affected systems offline and contain the spread of attackers. This step is crucial to minimize the damage done to your systems and organization, according to the CSO article “The Six Stages of Incident Response.”
This stage of incident response includes both short- and long-term containment activities. Visit the SANS Institute website for more details on what this phase involves, such as changing passwords, killing backdoors, and more.
7. Work on eradication. After you’ve stopped the cyberattack from spreading, you can move on to eradicating the threat. Eradication involves steps such as deleting artifacts, applying patches, changing DNS names, removing malware, and rescanning the network, according to SANS.
8. Recover and restore systems. Following eradication, you should take actions related to recovery and restoration. This will involve figuring out when you can bring your system back into production, as well as how long you should monitor it for unusual activity, according to CSO.
9. Reflect on lessons learned. To reduce the risk of future breaches, it’s crucial to review what happened, learn from your mistakes and adjust your incident response process accordingly.
Your organization should record the entire procedure for reacting to a data breach in a policy document that everyone on staff is aware of and knows how to locate and follow in the event of a security incident. Additionally, even in the absence of breaches, you should regularly test and update your response plan.
If you have any questions about dealing with data breaches, don’t hesitate to contact our team of IT security experts. We offer a wide range of managed cybersecurity solutions from various vendors and can assist you in developing a comprehensive security strategy to minimize your risk of experiencing a breach. Contact us today by calling 877-599-3999 or emailing sales@stratospherenetworks.com.


